Python Tkinter - Complete GUI Guide
2026-02-10
Build desktop GUIs in Python with Tkinter, covering widgets, layouts, and events.
2120 words
|
11 minutes
Network Scanning and Enumeration Techniques
2026-02-07
Essential techniques for discovering and mapping network infrastructure and services
647 words
|
3 minutes

Understanding SQL Injection Vulnerabilities
2026-02-07
A comprehensive guide to one of the most critical web application security vulnerabilities
739 words
|
4 minutes

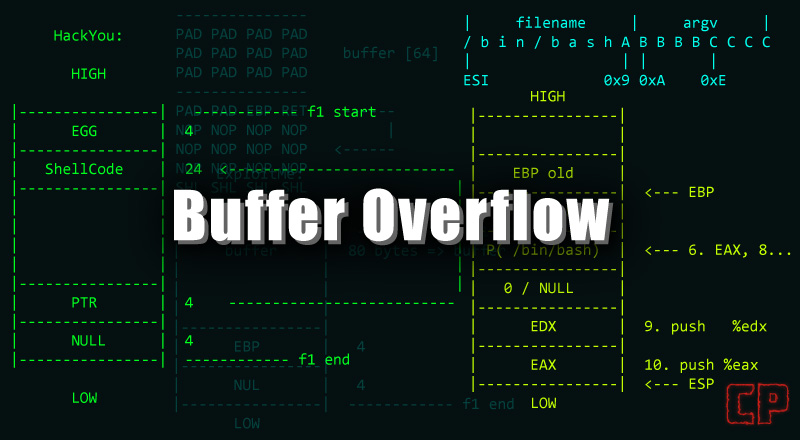
Understanding Buffer Overflow Vulnerabilities
2026-02-06
A deep dive into one of the most critical memory corruption vulnerabilities that attackers exploit to gain control of systems
903 words
|
5 minutes
Python pycryptodome Module - Complete Tutorial
2026-02-05
Practical guide to Python pycryptodome for encryption, hashing, and cryptography workflows.
631 words
|
3 minutes

Python hashlib Module - Complete Tutorial
2026-02-05
Practical guide to Python hashlib for hashing, integrity checks, and security workflows.
751 words
|
4 minutes

The Art of Reconnaissance Part 1 - How Hackers Find Vulnerabilities Before You Do
2026-02-05
Every successful cyber attack begins long before the first exploit is launched. It starts with reconnaissance
668 words
|
3 minutes

Python BeautifulSoup Module - Complete Tutorial
2026-02-05
Practical guide to Python BeautifulSoup for parsing HTML, extracting data, and web scraping workflows.
373 words
|
2 minutes

