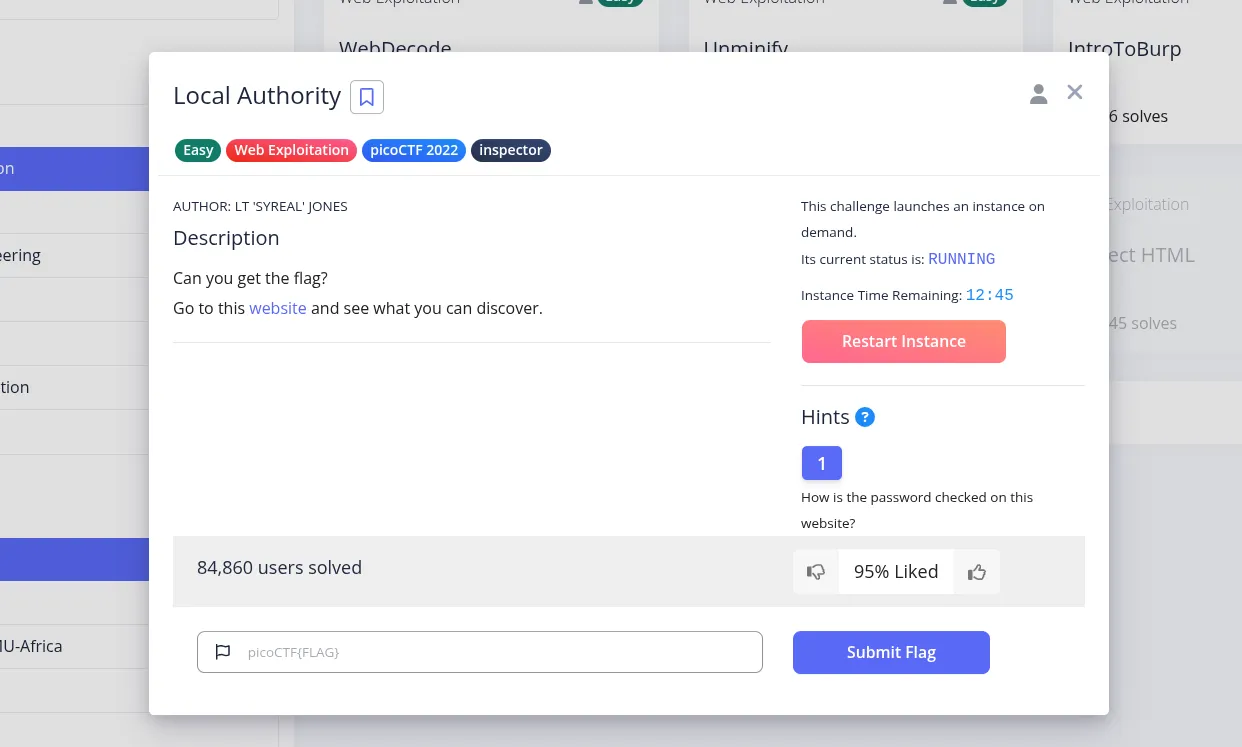
Local Authority - picoCTF Writeup
2026-04-12
A picoCTF web challenge focused on weak client-side authentication, where the valid credentials are exposed in a JavaScript file.
285 words
|
1 minute
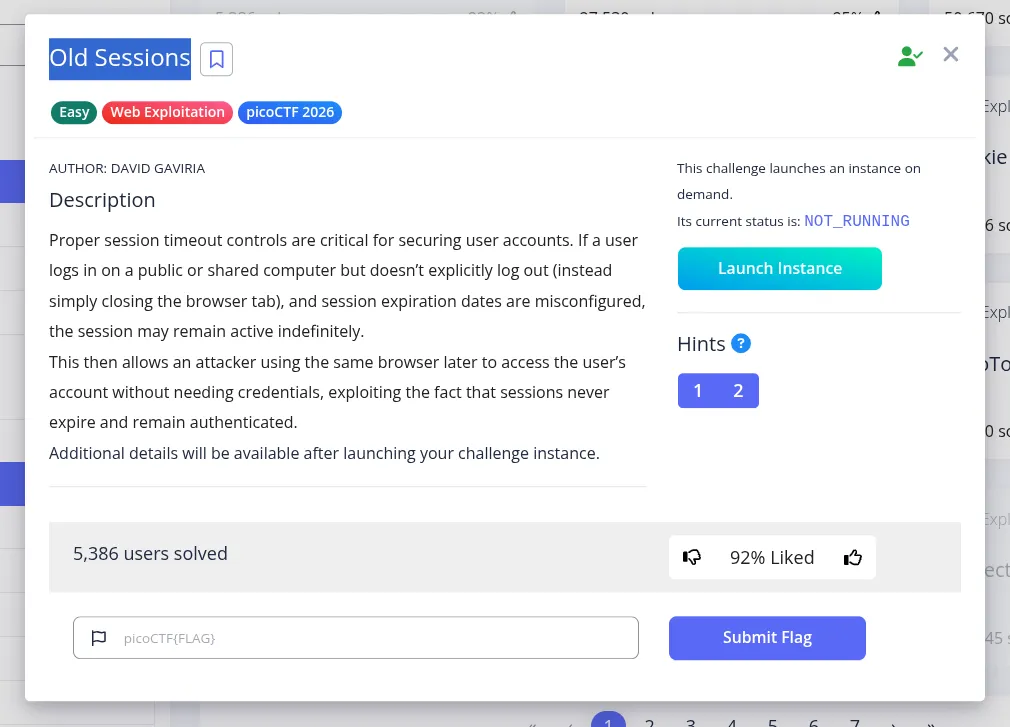
Old Sessions - picoCTF Writeup
2026-04-12
A picoCTF web challenge where exposed session data allows us to replace our cookie with an admin session and access the flag.
241 words
|
1 minute
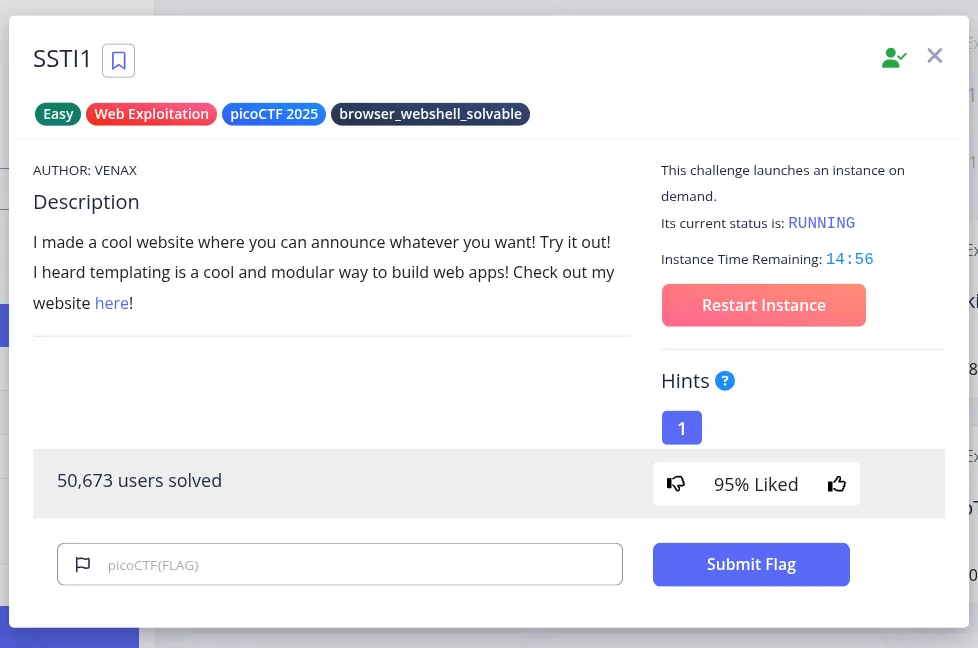
SSTI1 - picoCTF Writeup
2026-04-12
A picoCTF web challenge that demonstrates server-side template injection in a Flask application and leads to file disclosure through template execution.
282 words
|
1 minute
Bookmarklet - picoCTF Writeup
2026-04-12
A quick picoCTF web challenge where the flag is hidden inside a JavaScript bookmarklet and can be recovered by understanding the client-side decryption logic.
292 words
|
1 minute
WebDecode - picoCTF Writeup
2026-04-12
A beginner-friendly picoCTF web challenge where the flag is hidden in page source as Base64-encoded data.
174 words
|
1 minute
The Benarroch File CTF Writeup
2026-04-12
An OSINT challenge writeup that traces a real Interpol Red Notice subject through public company records to identify a last known 2015 address.
529 words
|
3 minutes

Operation Takeover TryHackMe Writeup
2026-04-11
A simple TryHackMe writeup for Operation Takeover covering Nmap, UDP discovery, SNMP enumeration, and reading the root flag through the NET-SNMP-EXTEND feature.
1019 words
|
5 minutes
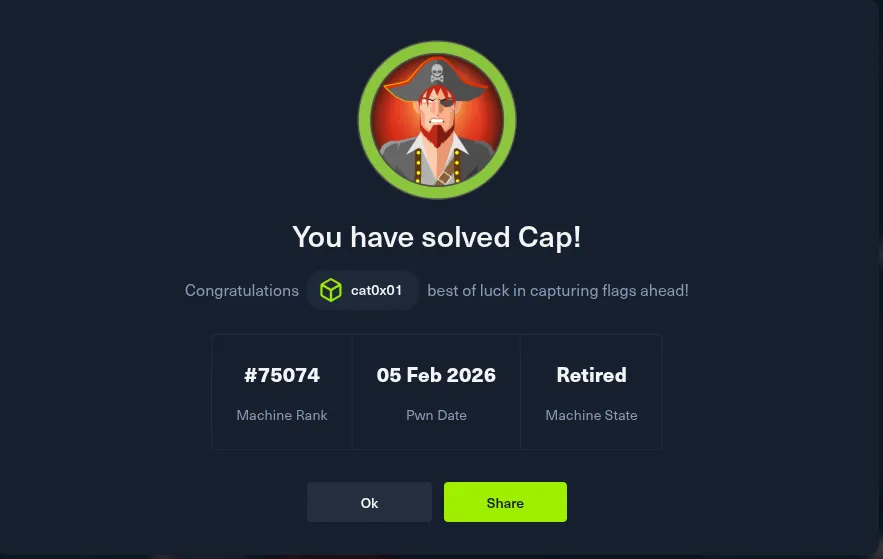
Cap Hack The Box Writeup
2026-04-10
A simple Hack The Box writeup for Cap covering Nmap enumeration, an IDOR issue in PCAP snapshots, credential recovery from FTP traffic, SSH access, and privilege escalation through Linux capabilities.
515 words
|
3 minutes