Overview
Dig Dug is an easy TryHackMe challenge focused on DNS enumeration.
The goal is to query a specific DNS server correctly in order to retrieve a hidden flag stored in a DNS record.
This room helps you understand how DNS queries work and how attackers can extract information from misconfigured DNS servers.
Target Information
- Challenge type: DNS / Enumeration
- Service: DNS
- Tools used:
dig,nslookup - Difficulty: Easy
Understanding the Hint
From the challenge description, an important hint is given:
The server only responds to requests for
givemetheflag.com
This tells us two critical things:
- We must query this exact domain
- We must send the query directly to the target DNS server
Querying random domains or using the system’s default DNS server will not work
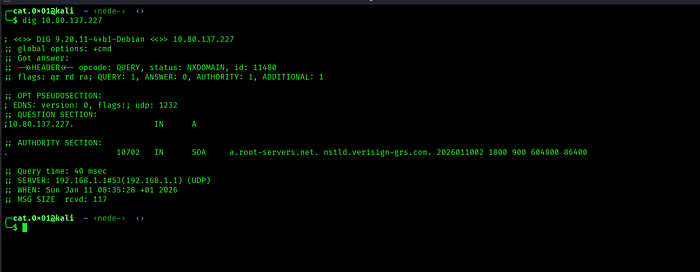
The response returns NXDOMAIN which means the query did not match any valid domain This confirms that the DNS server is online but it does not respond to generic queries
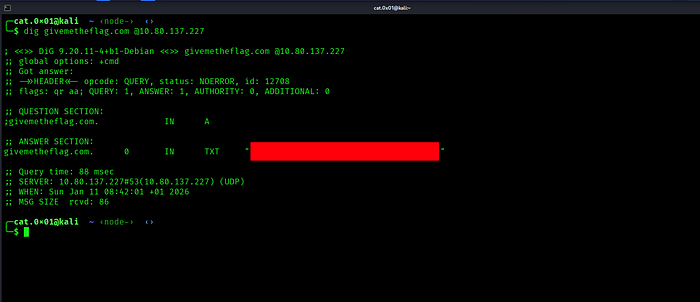
This command asks the target DNS server for records related to givemetheflag.com
After running the command, look at the ANSWER SECTION of the output

The value inside the TXT record is the flag
Why This Works
- The DNS server is configured to respond only to a specific domain
- The flag is stored inside a TXT DNS record
- Directly querying the server bypasses default DNS resolution
This is a common technique used during reconnaissance in penetration testing
I hope you enjoyed this challenge and found it interesting See you in the next one!
