We’re back with another TryHackMe challenge.
In this room we’re given a web application that looks simple at first glance but hides a vulnerability related to file inclusion and path traversal. Our goal is to deploy the machine access the web application and leverage this weakness to read files on the system until we locate the flag stored in the root directory
Let’s start by launching the machine and interacting with the target application
As usual we begin by running an Nmap scan to enumerate open ports and services on the target machine
nmap -sV -sC -sS 10.82.145.44Starting Nmap 7.95 ( https://nmap.org ) at 2026-01-08 01:13 +01Nmap scan report for 10.82.145.44Host is up (0.084s latency).Not shown: 998 closed tcp ports (reset)PORT STATE SERVICE VERSION22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.4 (Ubuntu Linux; protocol 2.0)| ssh-hostkey:| 3072 1d:41:7e:12:93:62:e5:1f:a1:5b:a9:05:0e:1a:4c:db (RSA)| 256 48:85:4a:32:8e:0a:5a:1e:2f:48:e1:37:20:60:d6:34 (ECDSA)|_ 256 30:59:7d:c8:6b:62:c3:60:60:51:98:d2:b2:ae:dd:00 (ED25519)80/tcp open http Apache httpd 2.2.22 ((Ubuntu))|_http-title: Lo-Fi Music|_http-server-header: Apache/2.2.22 (Ubuntu)Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 18.49 secondsThe results show that ports 22 (SSH) and 80 (HTTP) are open
Since a web service is available our next step is to browse the website on port 80 and examine its content more closely to see how the application behaves and whether it exposes any potential weaknesses

When clicking on any category from the sidebar such as Relax we notice that the page loads content using a URL parameter :
page=relax.php
This indicates that the application dynamically includes files based on user input Since the value of the page parameter is directly reflected in the URL it becomes a strong candidate for Local File Inclusion (LFI) testing If proper validation is missing we may be able to manipulate this parameter to load arbitrary files from the system
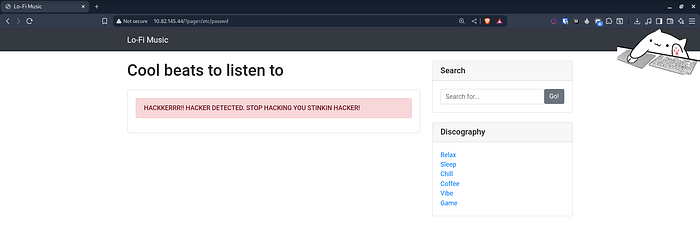
We first tried to access /etc/passwd directly using the page parameter as a test but the application returned a warning message indicating that the request was blocked This suggests that a basic filter is in place to prevent direct file access
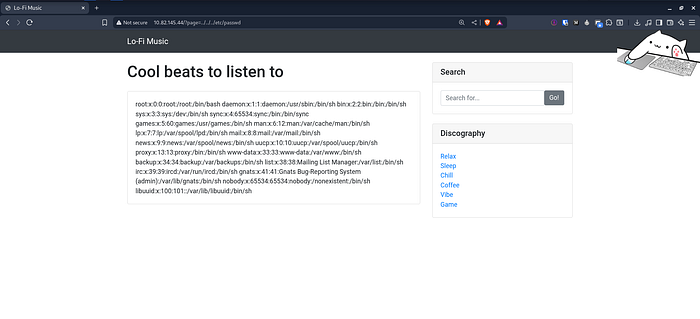
To bypass this restriction we experimented with simple path traversal payloads by moving up multiple directories. When using the following payload :
http://10.82.145.44/?page=../../../etc/passwdthe request was successful and the contents of /etc/passwd were displayed This confirms that the application is vulnerable to LFI and that the filtering mechanism can be bypassed using directory traversal techniques
After some further enumeration we tried accessing /root/flag.txt but the file was not found Continuing our search we discovered that the flag file was actually located directly in the root directory at /flag.txt which we were able to read successfully
http://10.82.145.44/?page=../../../flag.txt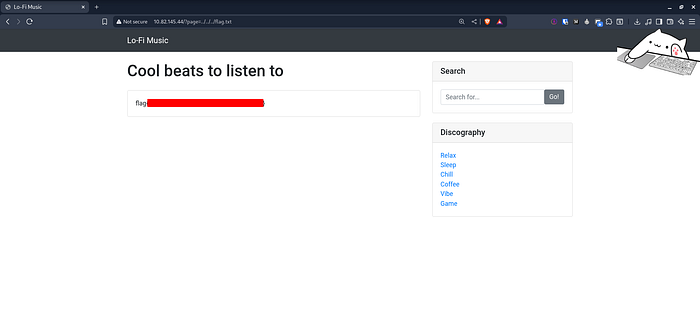
And with that we’ve successfully completed the challenge I hope you enjoyed it and I’ll see you again in a new challenge
X : https://x.com/cat0x01Github : https://github.com/cat0x01