Hi All We’re back with another challenge called Neighbour
Link : https://tryhackme.com/room/neighbour
This is a beginner friendly CTF about IDOR.
This challenge demonstrates a classic IDOR vulnerability. Poor access control allows attackers to modify user input and access resources they are not authorized to view
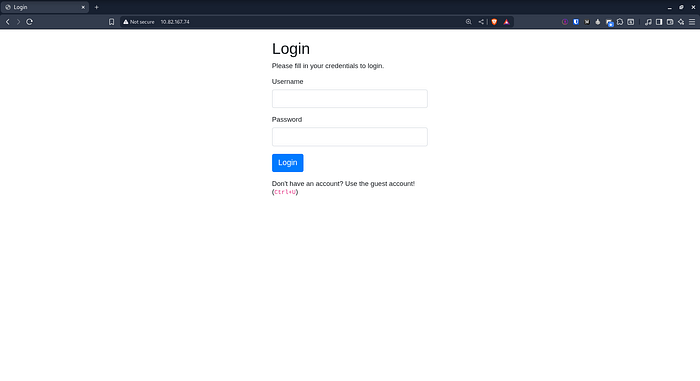
We start the challenge and browse to the target IP address As expected we are automatically redirected to the login page.
The challenge hints at using the Ctrl + U shortcut to inspect the page source code
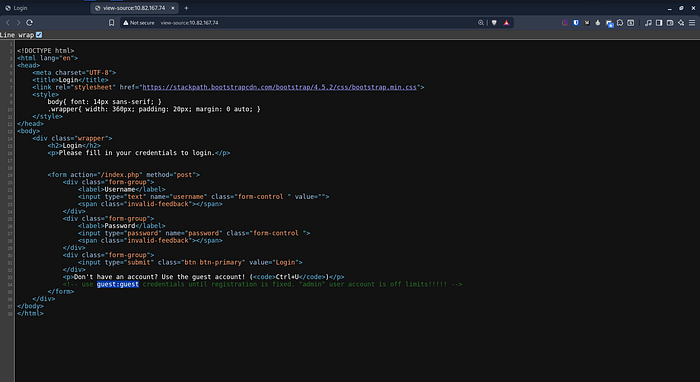
The source code reveals a comment suggesting the use of guest
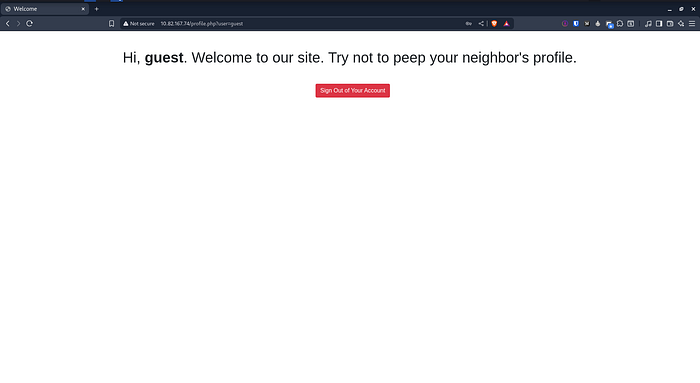
After logging in we found another comment in the source code indicating that the admin account might be vulnerable
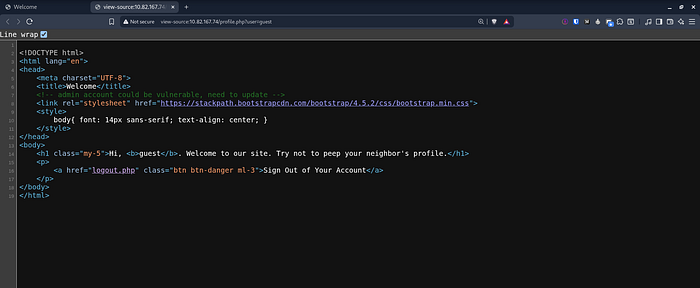
This message suggests a possible access control issue involving the admin account which aligns with the IDOR of the challenge
Since this lab focuses on IDOR we start paying close attention to how user data is handled in the URL After logging in as guest, we notice the following endpoint :
http://10.82.167.74/profile.php?user=guestThe user parameter is user controlled which means we can try modifying it When we change the parameter from guest to admin we are able to access the admin profile without proper authorization.
http://10.82.167.74/profile.php?user=adminThis confirms the presence of an IDOR vulnerability where the application fails to enforce proper access control and allows unauthorized access to another user’s data

As you can see we were able to obtain the flag very easily and This lab clearly shows how dangerous IDOR vulnerabilities can be even in very simple applications
I hope you enjoyed this simple lab and I’ll see you in a new challenge
x : https://x.com/cat0x01github : https://github.com/cat0x01