In this challenge, we are given an image and asked to use OSINT techniques to answer a set of questions.
At the beginning of the challenge, we were given an image file.
Since this is an OSINT challenge, the first logical step is to check if the image contains hidden metadata.

We used the tool exiftool to extract EXIF information from the image.
exiftool WindowsXP_1551719014755.jpg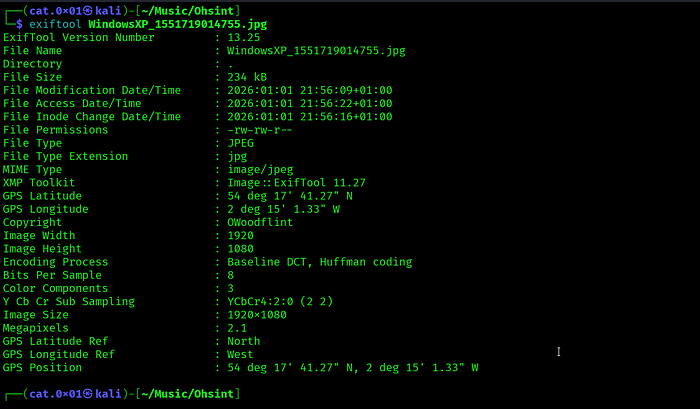
Important Findings
While reviewing the output, some information immediately caught our attention :
The image contains GPS data :
Latitude: 54° 17’ 41.27” N
Longitude: 2° 15’ 1.33” W
This means the photo was taken at a specific real world location, which is very useful in OSINT investigations
Another interesting field was :
Copyright : OWoodflintThis looks like a username or real name and it can be used as a pivot for further OSINT searches on Google , Social media platforms , Image search
, Username enumeration
To continue the investigation, we searched for the name OWoodflint using google
As a first step in the search , I found an X (Twitter) account related to the target
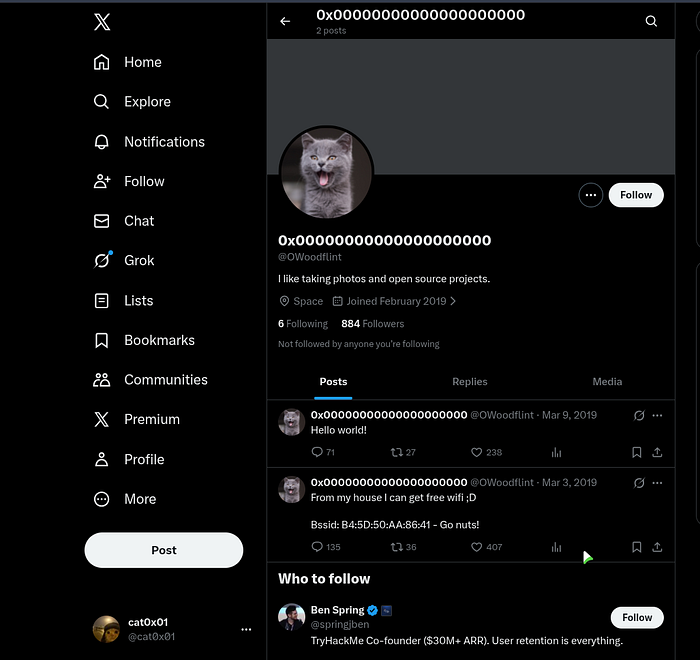
Q1 : What is this user’s avatar of ?
Answer : cat
I also found a GitHub repository using the same username
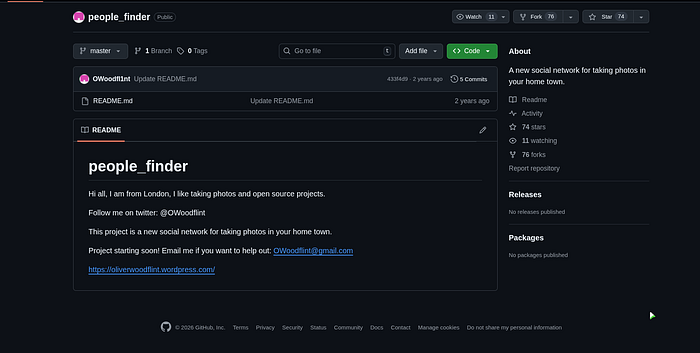
Q2 : What city is this person in?
Answer : London
Q4 : What is his personal email address?
Answer : OWoodflint@gmail.com
Q5 : What site did you find his email address on?
Answer : github

The target leaked their Wi-Fi BSSID on Twitter. I used this BSSID on Wigle.net by performing an advanced search. After entering the BSSID Wigle returned the network information
Q3 : What is the SSID of the WAP he connected to?
Answer : UnileverWifi
In the previously discovered repository, we found a link to the target’s personal webpage. I visited the page, as shown in the screenshot below
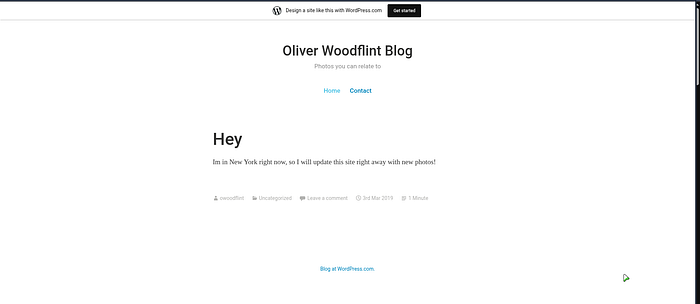
We determined that the target is currently located in New York
Q6 : Where has he gone on holiday?
Answer : New York
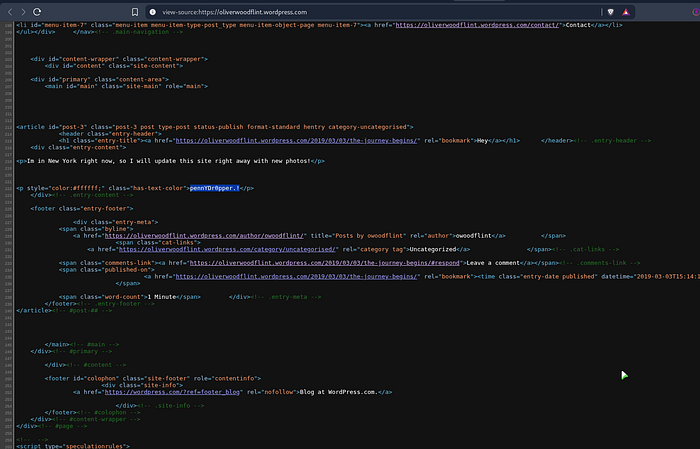
As mentioned in the TryHackMe question about the password of user, many people whether developers or regular users often make critical security mistakes by leaving sensitive information such as passwords inside code comments
I performed a thorough review of the source code, and after careful inspection, I was able to discover the target’s password
Q7 : What is the person’s password?
Answer : pennYDr0pper.!
We successfully completed the challenge. I hope you enjoyed it as much as I did it was simple and enjoyable. See you in future challenges
This challenge shows how small mistakes in online presence can lead to serious information leaks. Simple actions like reusing usernames, leaking Wi-Fi data, or leaving sensitive information in code can expose more than expected. Always review what you share publicly and follow basic security hygiene
