Buffer overflows are one of the oldest and most dangerous memory problems. They still matter today because a small bug can allow full control of a program. This topic is essential for developers, security engineers, and anyone who works with low-level software.
What is a Buffer Overflow?
A buffer is a small area of memory used to store data. A buffer overflow happens when a program writes more data than the buffer can hold. The extra data spills into nearby memory. This can break the program and sometimes lets an attacker change how it runs.
Think of a buffer as a box with a fixed size. If you keep adding data without checking the size, the extra data will not disappear. It will overwrite whatever is stored next to the box.
Why It Still Matters
Many critical systems are built in C and C++. These languages are fast and powerful, but they rely on the programmer to handle memory safely. One small mistake in input handling can lead to a security bug. Even in modern software, legacy code, embedded devices, and performance-critical components still use these languages.
How It Happens
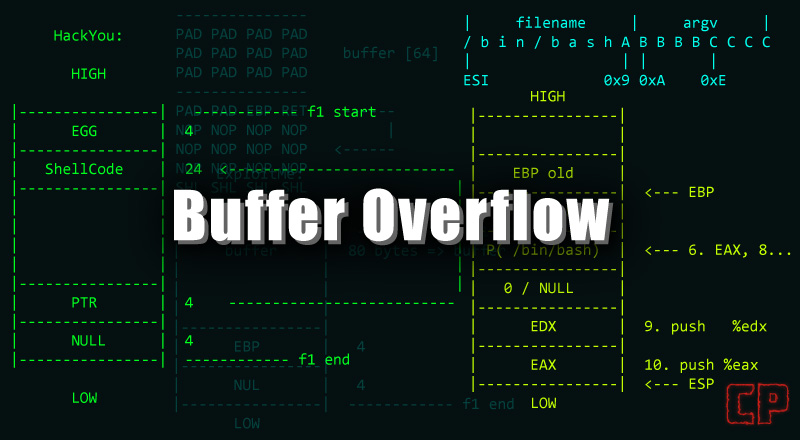
In low-level languages like C and C++, the programmer must manage memory manually. If input length is not checked, a program may write past the end of a buffer. This can overwrite important values like return addresses or function pointers.
Common reasons:
- No bounds checking
- Unsafe copy functions
- Trusting user input without validation
- Off-by-one errors in length calculations
- Incorrect assumptions about input format
Typical Places Where It Occurs
Buffer overflows often appear in areas that process external data:
- Network services that parse packets or requests
- File parsers that read large or malformed files
- Command-line tools that accept long arguments
- Authentication or logging code that handles user input
- Device firmware or embedded systems with limited checks
Code Example: Vulnerable vs Safe Input Handling
The unsafe version below does not check the length of the input. It can write past the buffer.
#include <stdio.h>#include <string.h>
void unsafe_copy(const char *input) { char buffer[16]; strcpy(buffer, input); // no bounds check printf("%s\n", buffer);}A safer version checks the size and ensures the buffer is null-terminated:
#include <stdio.h>#include <string.h>
void safe_copy(const char *input) { char buffer[16]; strncpy(buffer, input, sizeof(buffer) - 1); buffer[sizeof(buffer) - 1] = '\0'; printf("%s\n", buffer);}Code Example: Using Safer Functions
Prefer bounded functions or modern alternatives when possible:
#include <stdio.h>
void safe_format(const char *user) { char msg[64]; snprintf(msg, sizeof(msg), "Hello, %s", user); printf("%s\n", msg);}Stack vs Heap Overflows
Stack overflow happens when a buffer on the stack is too small. This can overwrite the return address and change program flow. Stack overflows are classic and often easier to detect.
Heap overflow happens in dynamically allocated memory. It is often harder to exploit but can still lead to code execution or data corruption. Heap overflows may allow an attacker to corrupt heap metadata or overwrite important pointers.
Why It’s Dangerous
A buffer overflow can allow an attacker to:
- Crash a program (denial of service)
- Read or change sensitive data
- Run arbitrary code
- Take full control of a system
In some cases, the impact is limited to a crash. In other cases, a carefully crafted input can lead to full remote control. The impact depends on where the overflow occurs, what data is overwritten, and which defenses are enabled.
How Attackers Think About It
Attackers try to:
- Control the overwritten data
- Redirect execution flow
- Bypass protections like ASLR or NX
- Use existing code sequences already in memory
If an attacker can reliably control the program flow, the bug becomes a serious security risk.
Common Protection Techniques
Modern systems add protections that make exploitation harder:
- Stack canaries
- Address randomization (ASLR)
- Non-executable memory (NX/DEP)
- Safer standard libraries
- Control-flow integrity (CFI) on some platforms
These do not remove the bug, but they reduce the chance of successful exploitation. A well-protected system can still be vulnerable if the overflow is severe or if the attacker can chain multiple bugs.
Signs and Symptoms
Buffer overflows often show up as:
- Random crashes with no clear reason
- Unusual behavior after long or unexpected input
- Memory access errors or segmentation faults
- Security alerts triggered by abnormal execution
These are not proof of a buffer overflow, but they are strong signals to investigate memory safety.
Detection and Testing
Security teams and developers use multiple approaches:
- Static analysis tools to spot risky code paths
- Dynamic analysis and fuzzing to trigger crashes
- Runtime sanitizers to catch out-of-bounds writes
- Code reviews focused on input handling
Fuzzing is especially effective because it can discover edge cases that are hard to predict manually.
Prevention Tips
For developers:
- Validate input length and format early
- Use safer APIs that check bounds
- Avoid manual memory copies when possible
- Enable compiler protections and warnings
- Use sanitizers during testing
- Prefer memory-safe languages when possible
For system administrators:
- Keep software updated
- Enable OS hardening features
- Monitor for abnormal crashes or behavior
- Reduce exposed services to limit attack surface
Responsible Security Practice
Understanding buffer overflows is important for defense. Use this knowledge in safe environments such as test labs or training platforms. Never attempt exploitation on systems you do not own or have permission to test.
Learning Path
To learn this topic well, focus on:
- Memory layout (stack, heap, and stack frames)
- How function calls work
- Basic assembly concepts
- Security protections and how they work
- Secure coding guidelines for C/C++
A solid foundation in these areas makes it easier to understand why bugs happen and how to prevent them.
Common Misconceptions
- “Protections make overflows irrelevant.” They help, but the bug is still real.
- “Only old software has these bugs.” Many modern programs still include them.
- “Crashes are harmless.” A crash may hide a serious exploit path.
Summary
Buffer overflows happen when programs write beyond buffer limits. They are dangerous because they can change program behavior and lead to full compromise. Good input validation and modern protections reduce the risk, but the safest approach is writing secure code from the start.
