This challenge begins like a normal web application. We create an account, log in, and then look for places where session handling might be weak.
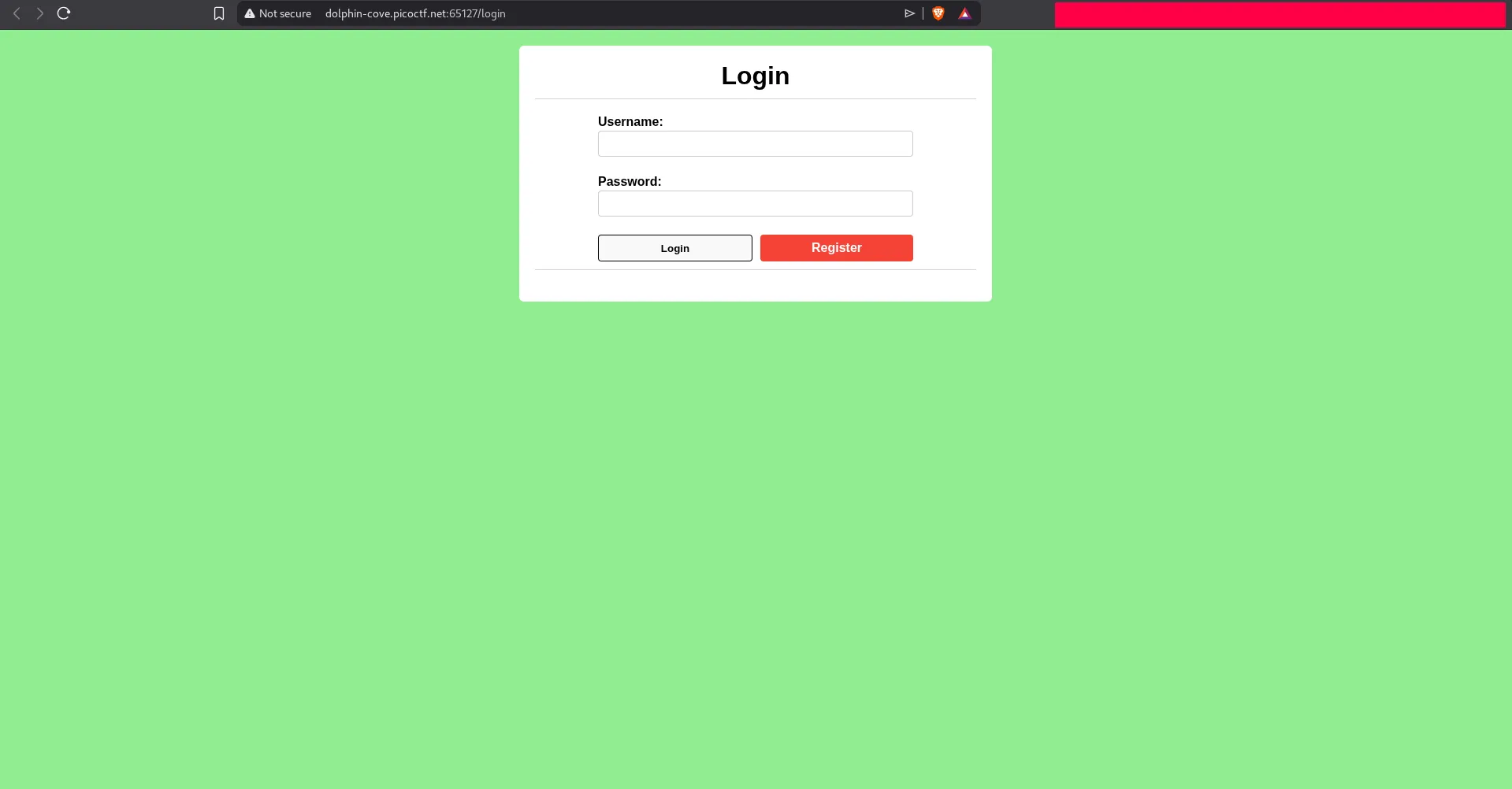
After registering and signing in, the page itself does not expose much. The source code is also not especially helpful, so the best move is to keep exploring the application and look for hidden routes or unusual hints.
Once logged in, we see a suspicious message:
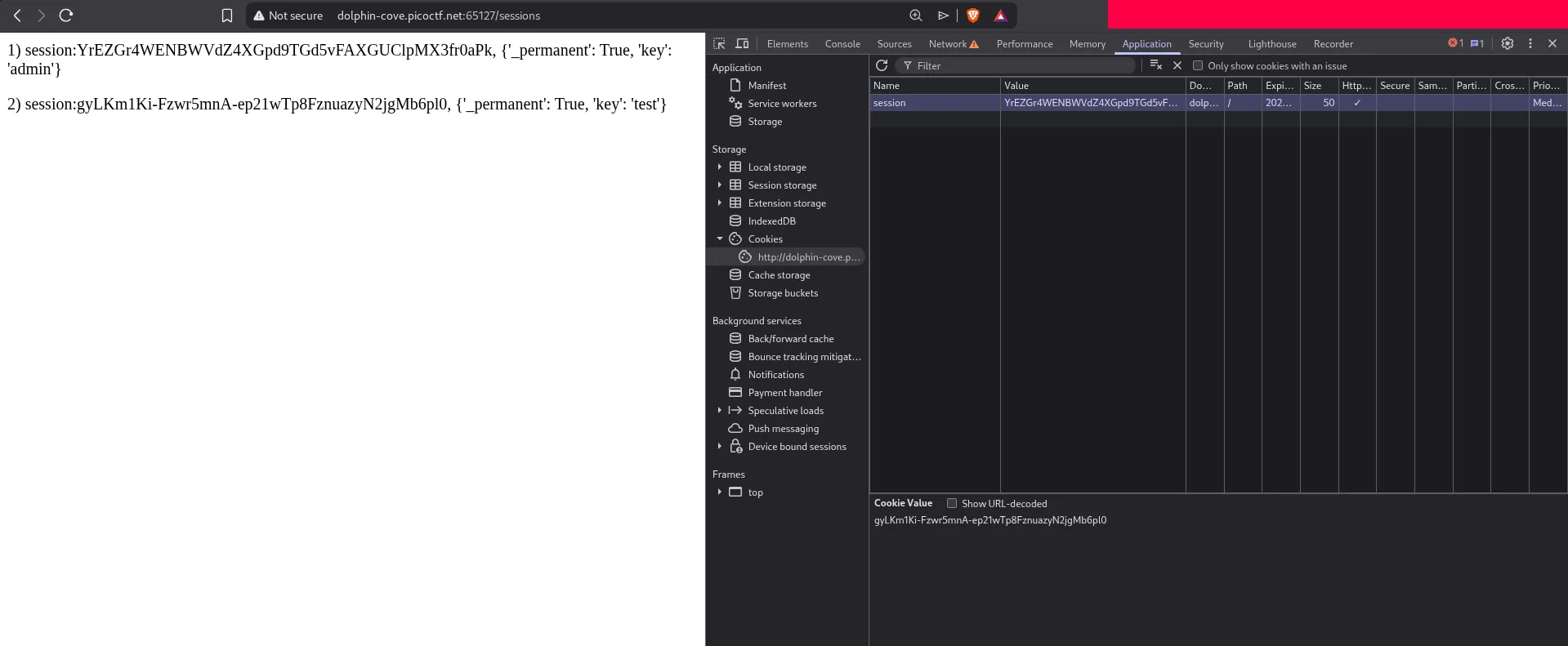
Hey I found a strange page at /sessions
That is the kind of hint picoCTF usually gives when the challenge wants us to inspect internal session behavior. So we visit /sessions.
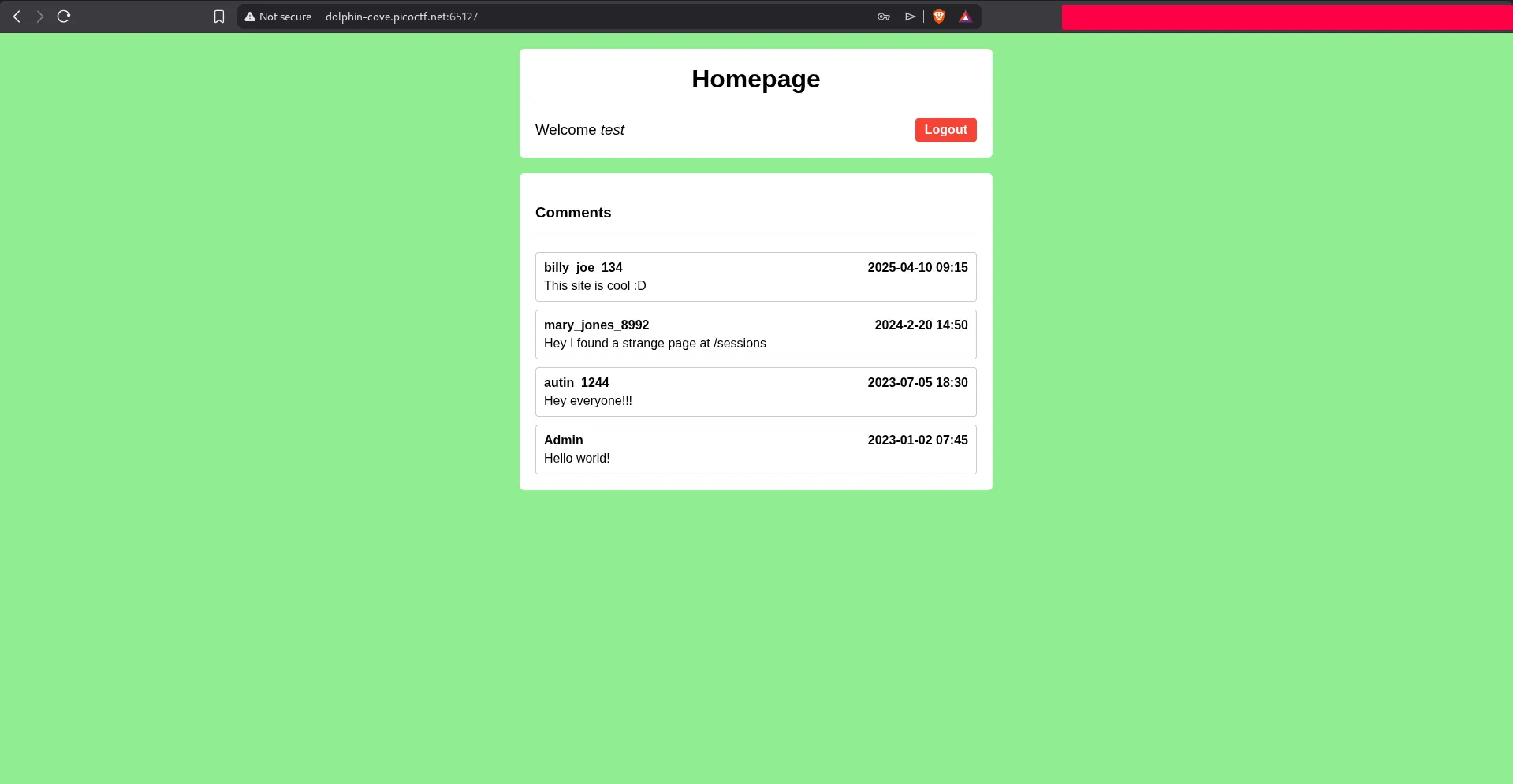
On that page, we discover session information that includes an admin session identifier. This is the core issue: the application exposes sensitive session data that should never be visible to normal users.
Exploitation Path
If we already control our own authenticated browser session, and we can see the admin session token, then the next step is straightforward:
- Open browser storage or cookie tools.
- Replace our current session value with the admin session value.
- Refresh the site so the application treats us as the admin user.
After swapping the cookie and reloading the page, the session is accepted as admin.
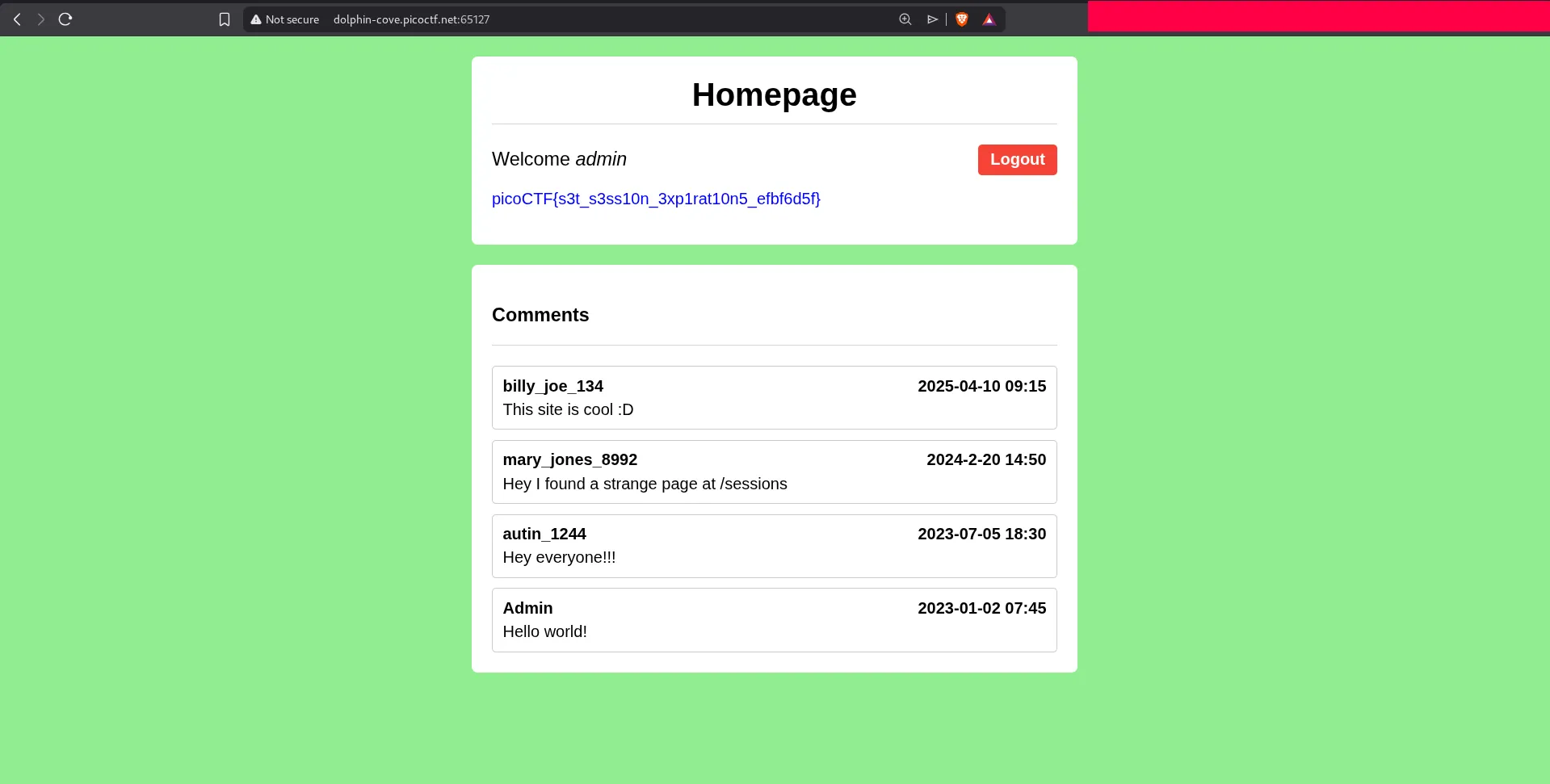
That gives us admin access and reveals the flag. Technically, this is a session management failure: the application leaks valid session identifiers and does not bind them strongly enough to the original user context.
