Dev Diaries
In this writeup, we solve the Dev Diaries room from TryHackMe using simple OSINT techniques. The challenge shows how old snapshots, public GitHub activity, and commit history can reveal sensitive information even after a site goes offline.
We start with the main domain, discover related subdomains, search archived versions of the website, identify the developer, and then inspect the repository history to recover the final flag.
Challenge Info :
We have just launched a website developed by a freelance developer. The source code was not shared with us, and the developer has since disappeared without handing it over.
Despite this, traces of the development process and earlier versions of the website may still exist online.
You are only given the website's primary domain as a starting point: marvenly.comWe begin by using subfinder to discover subdomains related to the target domain.
┌──(cat0x01㉿cat0x01)-[~]└─$ subfinder -d marvenly.com
__ _____ __ _______ __/ /_ / __(_)___ ____/ /__ _____ / ___/ / / / __ \/ /_/ / __ \/ __ / _ \/ ___/ (__ ) /_/ / /_/ / __/ / / / / /_/ / __/ //____/\__,_/_.___/_/ /_/_/ /_/\__,_/\___/_/
projectdiscovery.io
[INF] Current subfinder version v2.12.0 (outdated)[INF] Loading provider config from /home/cat0x01/.config/subfinder/provider-config.yaml[INF] Enumerating subdomains for marvenly.comadmin.marvenly.comuat-testing.marvenly.comwww.marvenly.com[INF] Found 3 subdomains for marvenly.com in 10 seconds 593 millisecondsWe found three subdomains. At the time of the challenge, the main website and the discovered subdomains were no longer active, but the names still give us useful clues.
What is the subdomain where the development version of the website is hosted?
Answer:
uat-testing.marvenly.com
Next, we use the Wayback Machine to look for older snapshots of the site while it was still online.
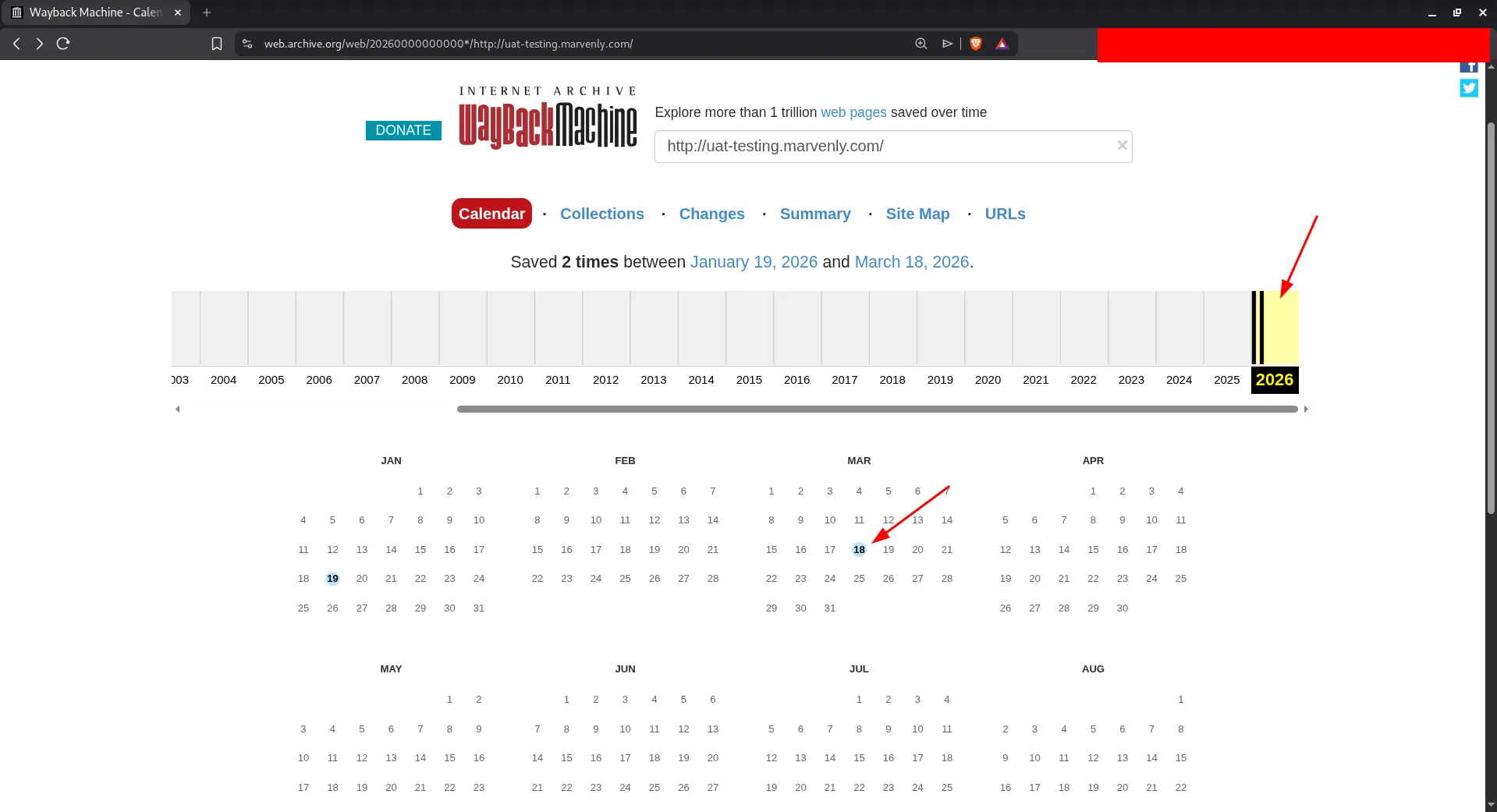
We found an archived screenshot of the website from March 18, 2026.
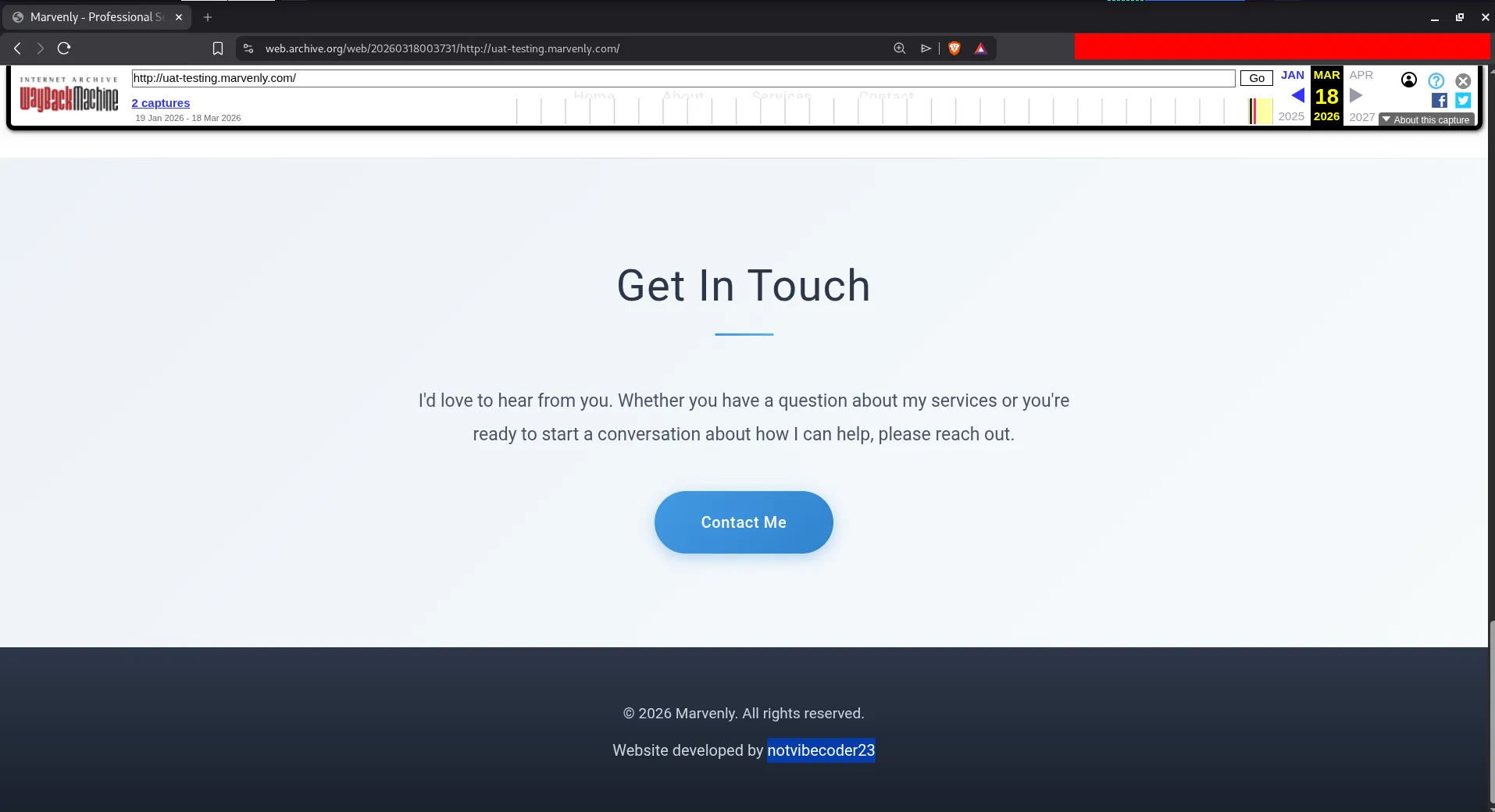
At the bottom of the archived page, we can see the name of the developer.
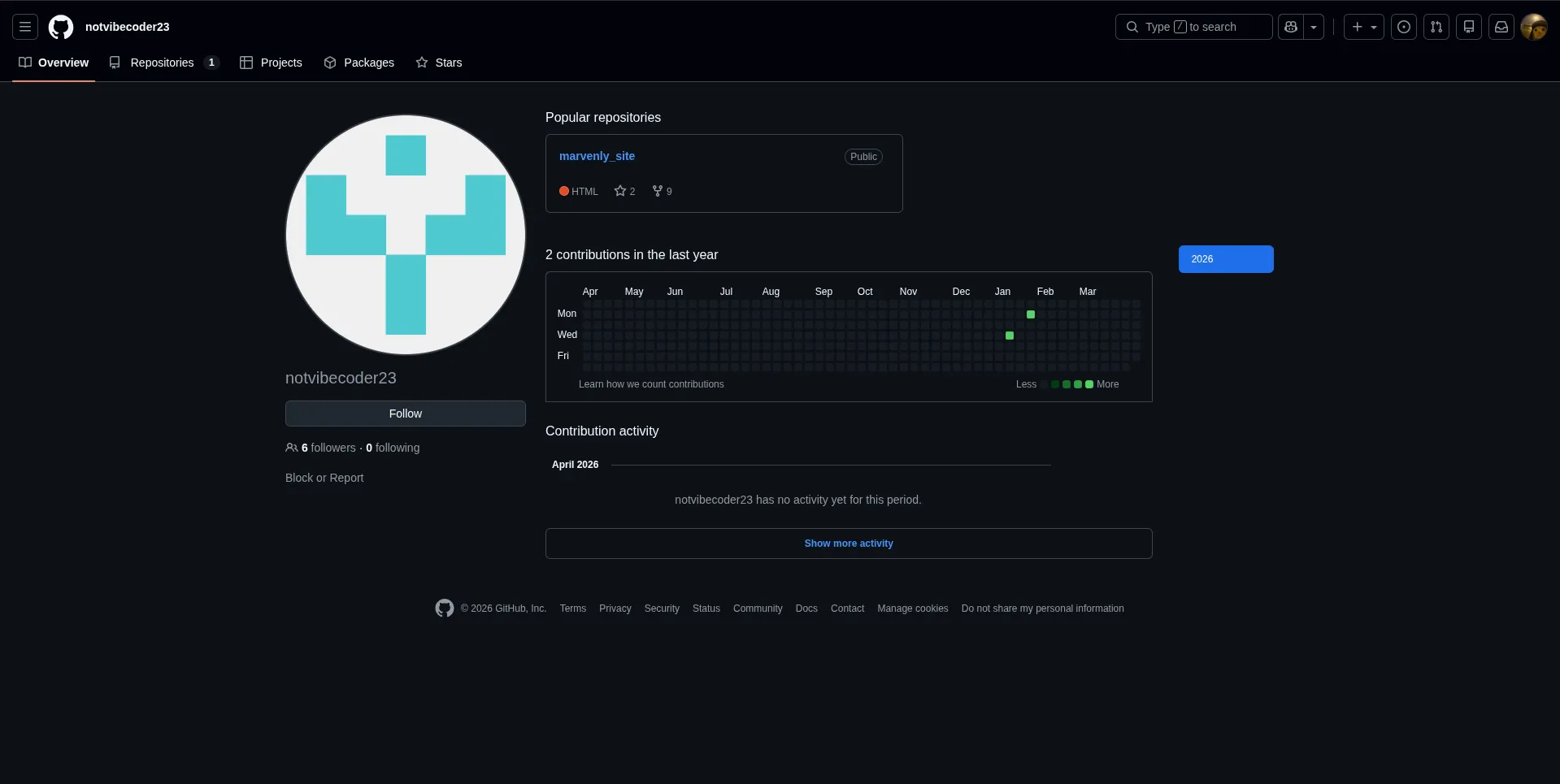
After searching for that name online, we find the GitHub account linked to the developer.
What is the GitHub username of the developer?
Answer:
notvibecoder23
The next task asks for the developer’s email address.
Inside the GitHub account, there is a repository related to the website, and it contains several commits. That means the commit history may expose more details than the latest version of the files.
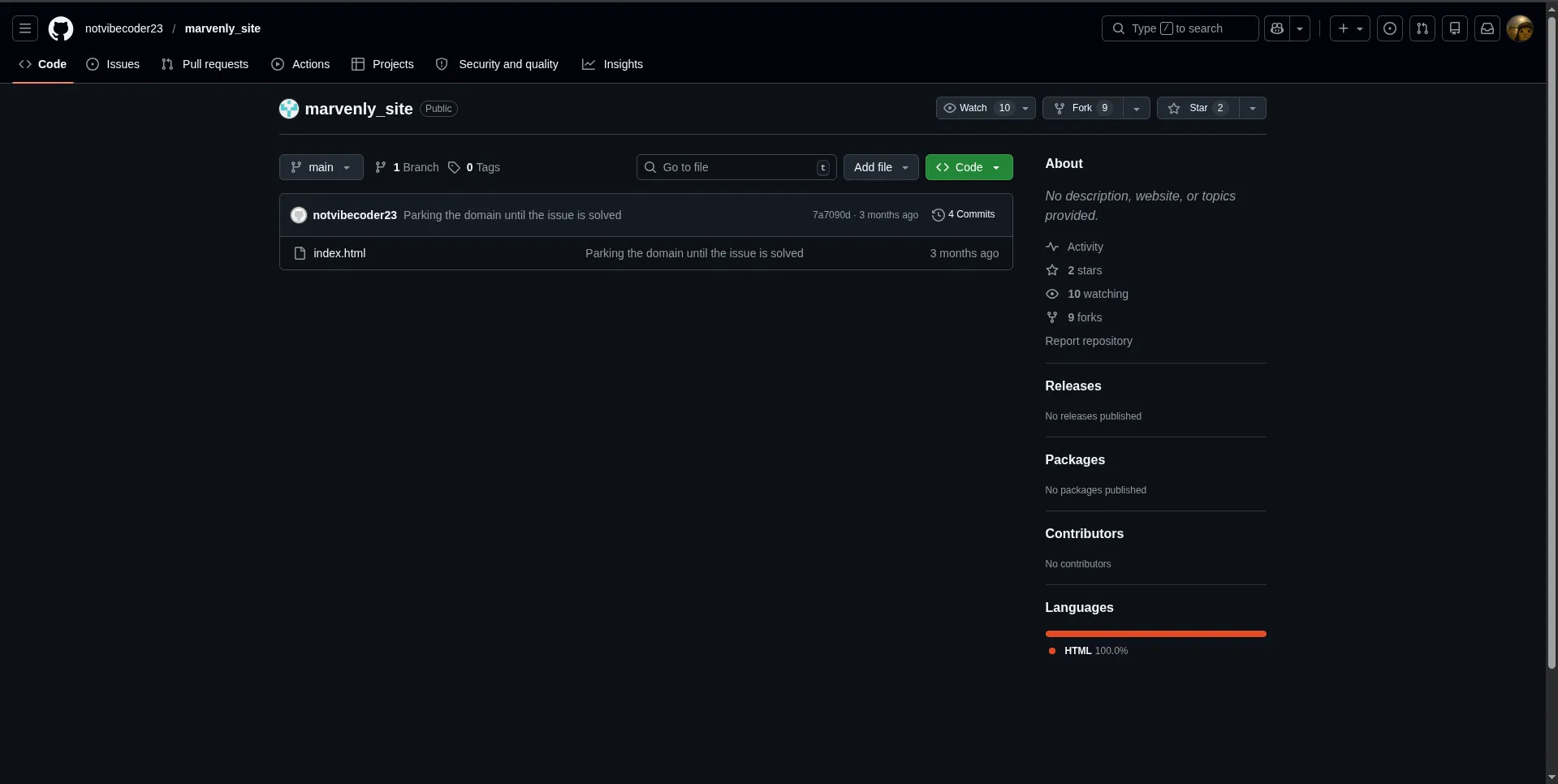
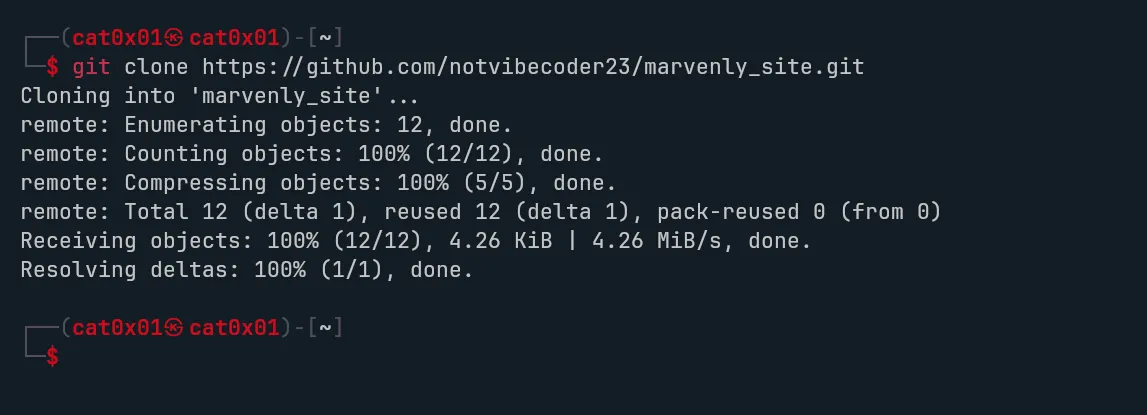
We download the repository and inspect it locally.
Now we review the available files.
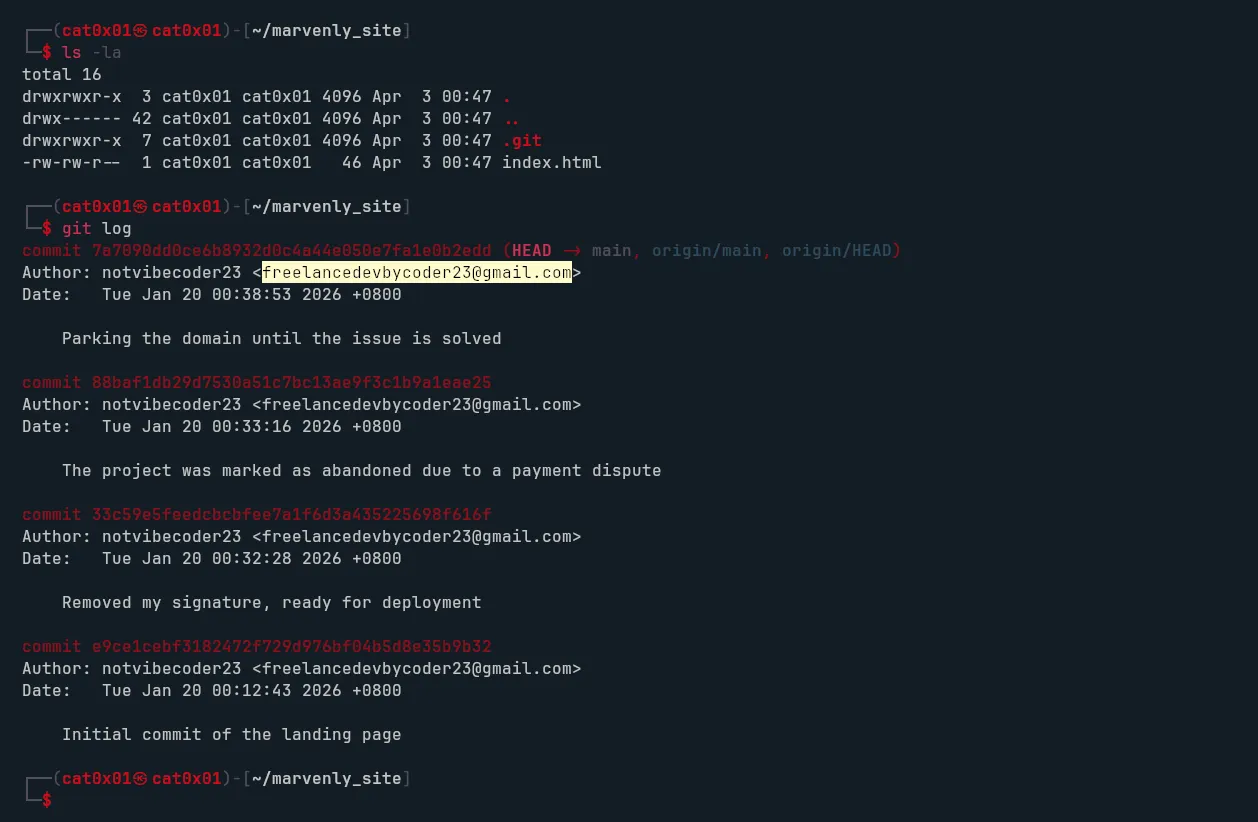
We notice that the repository still contains the .git directory, so we can inspect the commit history and author information. From there, we recover the developer’s email address.
What is the developer’s email address?
Answer:
freelancedevbycoder23@gmail.com
Another question asks why the developer removed the source code. The answer is clearly visible in one of the commit messages:
commit 88baf1db29d7530a51c7bc13ae9f3c1b9a1eae25Author: notvibecoder23 <freelancedevbycoder23@gmail.com>Date: Tue Jan 20 00:33:16 2026 +0800
The project was marked as abandoned due to a payment disputeAnswer:
The project was marked as abandoned due to a payment dispute
Next, we go back to the version where the developer wrote, Removed my signature, ready for deployment. This suggests that something was removed from index.html before the final version was published.
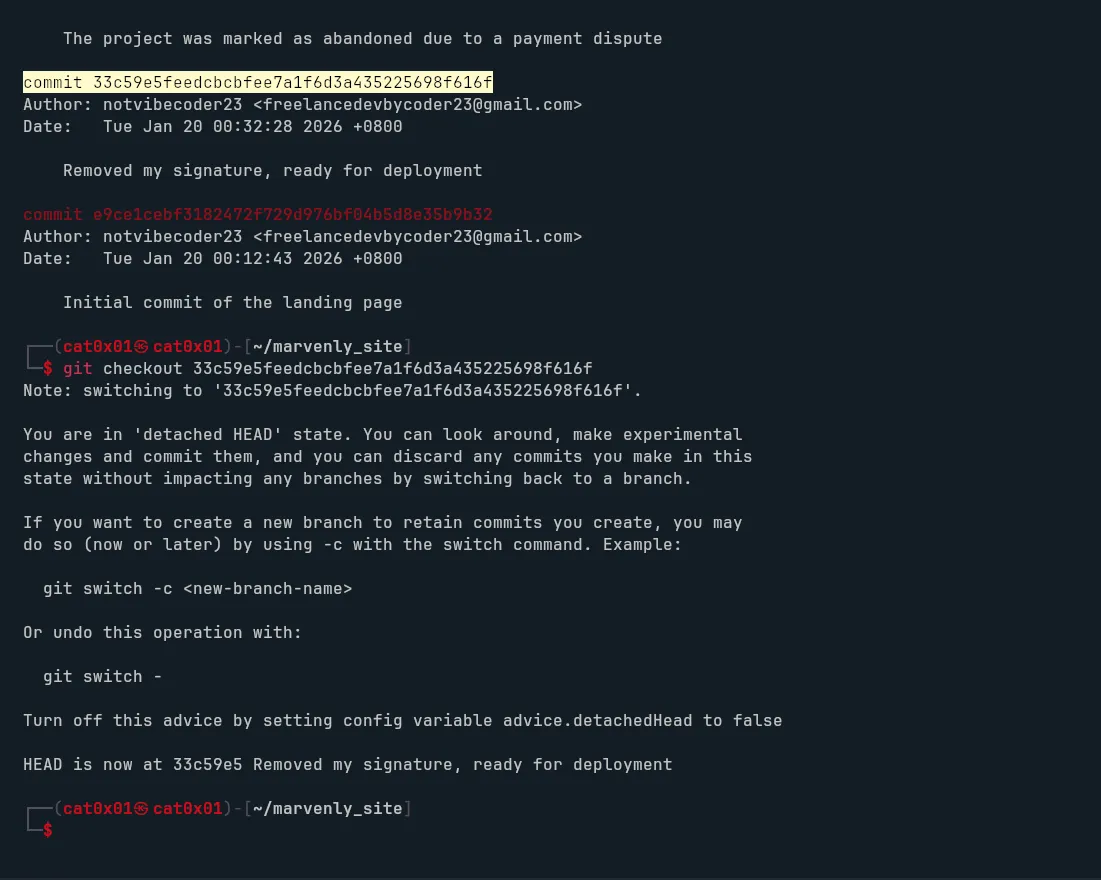
To verify that, we inspect the contents of index.html in that older commit.
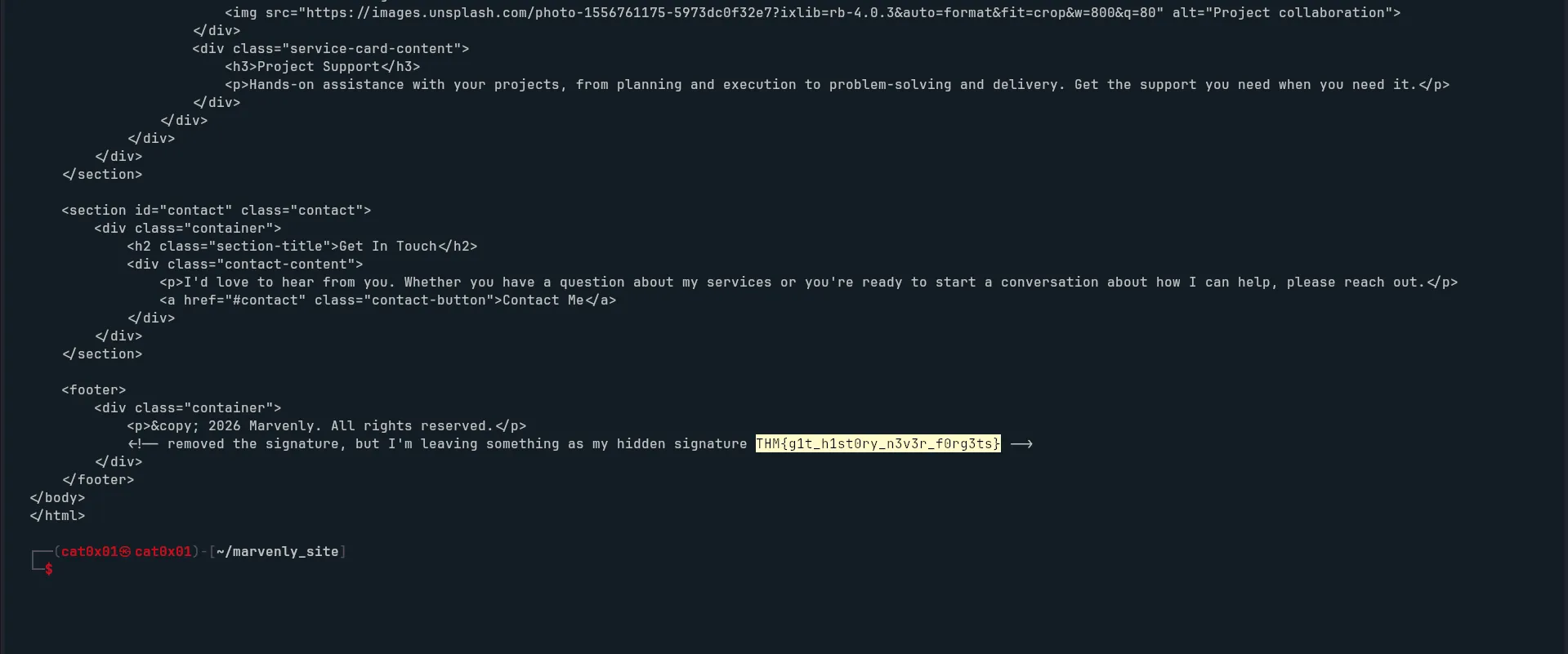
That reveals the hidden flag.
What is the value of the hidden flag?
Answer:
THM{g1t_h1st0ry_n3v3r_f0rg3ts}
This room is a good reminder that deleted content is not always really gone. Archived pages, exposed repository data, and old commits can all reveal information that developers thought had already disappeared.
Overall, Dev Diaries is a short but useful OSINT room for practicing subdomain discovery, archive research, GitHub investigation, and commit history analysis in a very practical way.
